Suppose you had deployed several microservices using Docker and you want to connect these microservices to the outside world. You will probably use some reverse proxy solution that will act as a frontend for these microservices. Nginx is the most popular and efficient reverse proxy solution, but it was written before container technology (like Docker) became so popular.
Say, for example, you want to remove one of the microservices from the container or change its port, and, as a result, you have to edit the Nginx configuration file to reflect the new container settings. Now, consider another situation where you add, delete, or scale the microservices application several times in a day—now, you’re editing the routes and other settings several times in the reverse proxy configuration file.
There’s a need for a new generation of reverse proxy solutions. Traefik is a modern reverse proxy solution written in GO to meet new these new containerized challenges.
“Træfik listens to your service registry/orchestrator API and instantly generates the routes so your microservices are connected to the outside world – without further intervention from your part.” Source: https://Traefik.io/
Traefik was developed with containerized technology in mind, which means there’s a lot of new features available in comparison with other reverse proxy solutions. When running, Traefik does the following and more:
- Dynamically updates the configuration and loads it without a restart.
- Load balances requests from the outside world using multiple available algorithms.
- Enables HTTPS for microservices using Let’s Encrypt.
- Provides a clean web UI.
- Supports for WebSocket, HTTP/2, GRPC.
- Provides metrics to Rest, Prometheus, Datadog, Statsd, InfluxDB.
In this article, we will check how to install Traefik and configure it in a standalone and Dockerized environment, and then give examples of connecting it to your microservices in the backend.
[cta_inline]
Prerequisites to install Traefik:
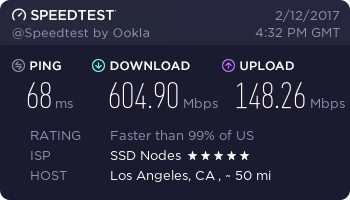
- A VPS running Ubuntu 16.04.
- A non-root,
sudo-enabled user. If you only have arootuser, see our SSH tutorial for details on creating new users. - A working Docker installation—for information about how to install Docker, check out our getting started with Docker tutorial
Step 1. Install Docker
To install the Docker use the following command.
$ sudo curl -sS https://get.docker.com/ | sh
The above command will update your system and install the correct version of docker.
Enable the docker service and start it.
$ sudo systemctl enable docker
$ sudo systemctl start docker
Step 2. Installing non-Dockerized backend applications
Our first goal is to route a few applications (backend) using Traefik (frontend) without Dockerizing them. To do that, we’ll install Apache and Nginx and configure them to use different ports, as they will act as a backend.
$ sudo apt-get install apache2
Change the port number to 8083 from 80 in /etc/apache2/ports.conf and restart Apache.
$ sudo vi /etc/apache2/ports.conf
$ sudo systemctl restart apache2
Install Nginx and change the port number to 8082 in the following two files. Then, restart Nginx.
$ sudo apt-get install nginx
$ sudo vi /etc/nginx/sites-available/default
$ sudo vi /etc/nginx/sites-enabled/default
$ sudo systemctl restart nginx
Now both Apache and Nginx will be available in the port number 8083 and 8082, respectively.
Continue reading this article
by subscribing to our newsletter.Subscribe now
A note about tutorials: We encourage our users to try out tutorials, but they aren't fully supported by our team—we can't always provide support when things go wrong. Be sure to check which OS and version it was tested with before you proceed.
If you want a fully managed experience, with dedicated support for any application you might want to run, contact us for more information.
by subscribing to our newsletter.
A note about tutorials: We encourage our users to try out tutorials, but they aren't fully supported by our team—we can't always provide support when things go wrong. Be sure to check which OS and version it was tested with before you proceed.
If you want a fully managed experience, with dedicated support for any application you might want to run, contact us for more information.