Secure Shell (SSH) is a fundamental component to virtual private servers (VPSs) and, generally speaking, Linux administration. The ability to connect two machines over a secure channel is invaluable, particularly when appropriately done with public keys, and many talented developers have bootstrapped SSH to build excellent tools like rsync.
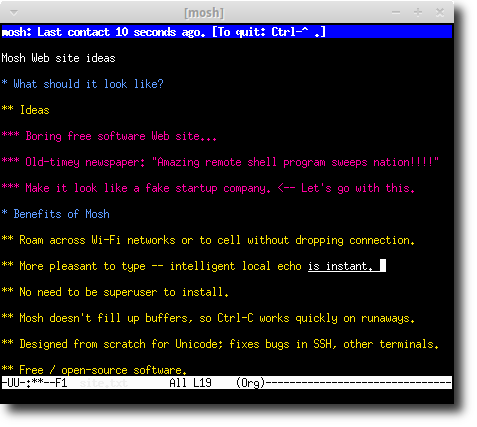
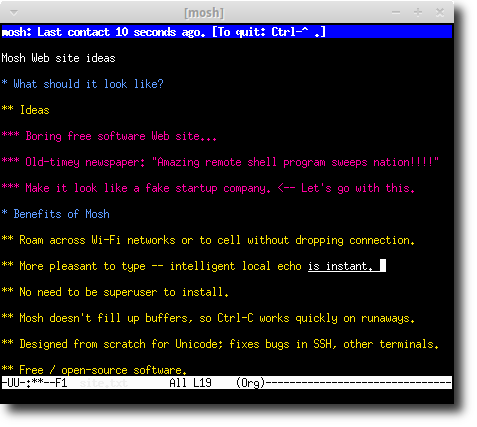
But SSH isn’t perfect. And there’s room for other tools with slightly different goals, or tools that aim to push SSH’s key benefits even further. Enter Mosh, the “mobile shell,” which, according to its developers, “allows roaming, supports intermittent connectivity, and provides intelligent local echo and line editing of user keystrokes.”
 Mosh is meant to be a complete replacement for SSH, and focuses on providing a more robust connection, particularly over spotty internet connections. If you want to get started with the tutorial part of this post right away, hop down to the first step.
Mosh is meant to be a complete replacement for SSH, and focuses on providing a more robust connection, particularly over spotty internet connections. If you want to get started with the tutorial part of this post right away, hop down to the first step.
[cta_inline]
 Mosh is meant to be a complete replacement for SSH, and focuses on providing a more robust connection, particularly over spotty internet connections. If you want to get started with the tutorial part of this post right away, hop down to the first step.
Mosh is meant to be a complete replacement for SSH, and focuses on providing a more robust connection, particularly over spotty internet connections. If you want to get started with the tutorial part of this post right away, hop down to the first step.
What’s wrong with SSH, again?
It’s not graceful on spotty connections. Well, sometimes SSH is terrible even when you’re using extremely reliable internet. That’s because when the connection between client and server falters, even momentarily, it can stall entirely, forcing you to kill it and reconnect. This process is annoying once, but after dozens of repetitions, it’s a real annoyance and leech on your time. SSH has a few security vulnerabilities. No piece of software is infallible, and SSH is no different—over the last two decades, security experts have discovered a few vulnerabilities in the SSH protocol, including a little something the NSA worked up. Despite these, SSH remains the most popular and respected method of connecting Network latency leads to lackluster typing performance. When you type into a terminal running an SSH connection, the client sends data about each keystroke to the remote server, which responds in kind. Only once the data has traveled to theContinue reading this article
by subscribing to our newsletter.
Subscribe nowby subscribing to our newsletter.
A note about tutorials: We encourage our users to try out tutorials, but they aren't fully supported by our team—we can't always provide support when things go wrong. Be sure to check which OS and version it was tested with before you proceed.
If you want a fully managed experience, with dedicated support for any application you might want to run, contact us for more information.




